Posted by Vineet Buch, Director of Product Management, Google Play Apps & Games
Recognizing the best
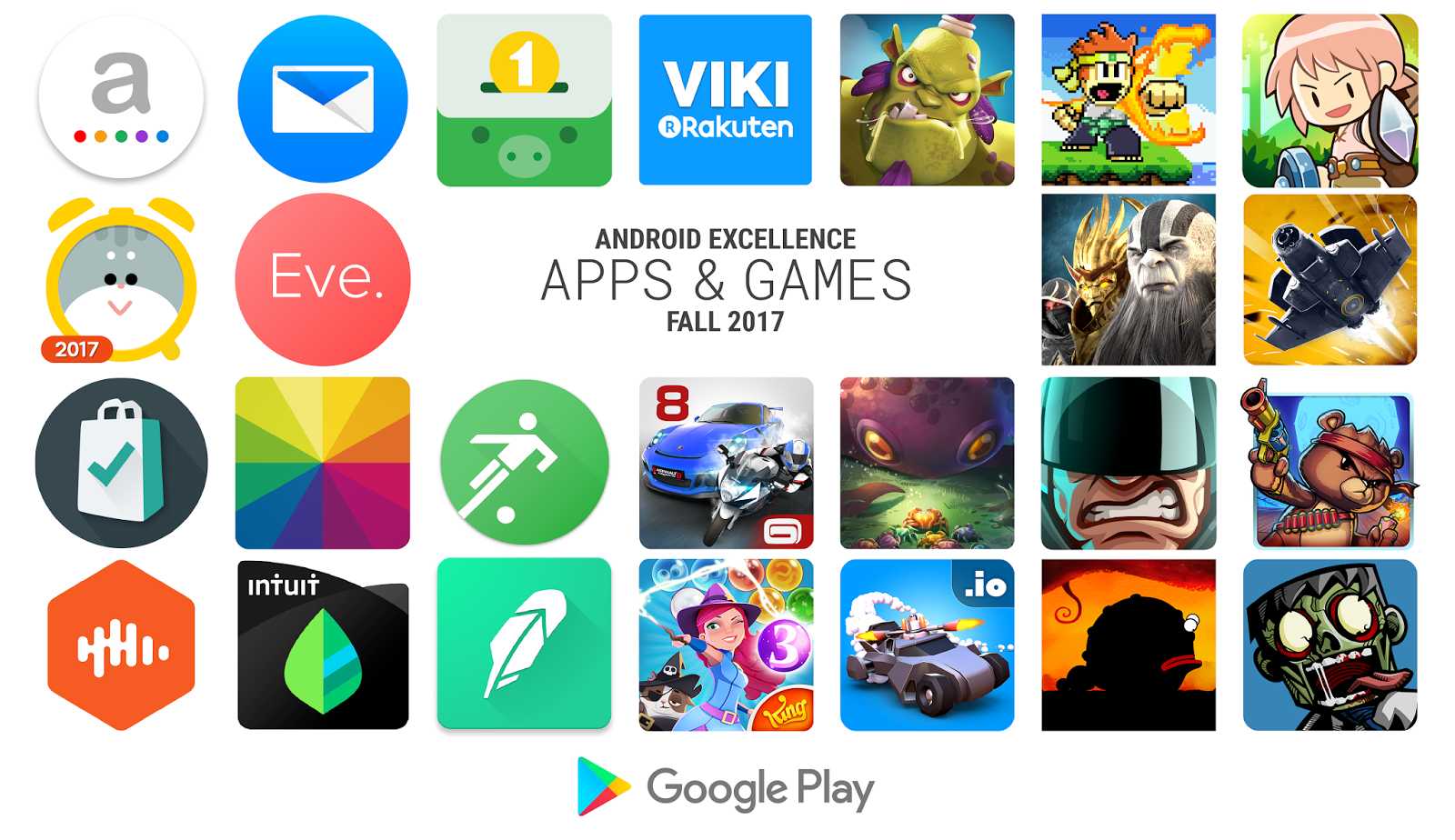
We're investing in curation and editorial to showcase the highest quality apps and games we love. The revamped Editors' Choice is now live in 17 countries and Android Excellence recently welcomed new apps and games. We also continue to celebrate and support indie games, recently announcing winners of the Indie Games Festival in San Francisco and opening the second Indie Games Contest in Europe for nominations.
Discovering great games
We've launched an improved home for games with trailers and screenshots of gameplay and two new browse destinations are coming soon, 'New' (for upcoming and trending games) and 'Premium' (for paid games).
Going beyond installs
We’re showing reminders to try games you’ve recently installed and we’re expanding our successful ‘live operations’ banners on the Play Store, telling you about major in-game events in popular games you’ve got on your device. We're also excited to integrate Android Instant Apps with a 'Try it Now' button on store listings. With a single tap, people can jump right into the app experience without installing. 

Focus on quality
Android vitals were introduced at I/O 2017 and already 65% of top developers are using the dashboard to understand their app's performance. We're adding five new Android vitals and increasing device coverage to help you address issues relating to battery consumption, crashes, and render time. Better performing apps are favored by Google Play's search and discovery algorithms.We're improving pre-launch reports and enabling them for all developers with no need to opt-in. When you upload an alpha or beta APK, we'll automatically install and test your app on physical, popular devices powered by Firebase Test Lab. The report will tell you about crashes, display issues, security vulnerabilities, and now, performance issues encountered.
When you install a new app, you expect it to open and perform normally. To ensure people installing apps and games from Google Play have a positive experience and developers benefit from being part of a trusted ecosystem, we are introducing a policy to disallow apps which consistently exhibit broken experiences on the majority of devices such as crashing, closing, freezing, or otherwise functioning abnormally. Learn more in the policy center.

Release with confidence
Beta testing lets trusted users try your app or game before it goes to production so you can iterate on your ideas and gather feedback. You can now target alpha and beta tests to specific countries. This allows you to, for example, beta test in a country you're about to launch in, while people in other countries receive your production app. We'll be bringing country-targeting to staged rollouts soon. We've also made improvements to the device catalog. Over 66% of top developers are using the catalog to ensure they provide a great user experience on the widest range of devices. You can now save device searches and see why a specific device doesn't support your app. Navigate to the device catalog and review the terms of service to get started.
Grow your subscriptions business
At I/O 2017 we announced that both the number of subscribers on Play and the subscriptions business revenue doubled in the preceding year. We're making it easier to setup and manage your subscription service with the Play Billing Library and, soon, new test instruments to simplify testing your flows for successful and unsuccessful payments. We're helping you acquire and retain more subscribers. You can offer shorter free trials, at a minimum of three days, and we will now enforce one free trial at the app level to reduce the potential for abuse. You can opt-in to receive notifications when someone cancels their subscription and we're making it easier for people to restore a canceled subscription. Account hold is now generally available, where you can block access to your service while we get a user to fix a renewal payment issue. Finally, from January 2018 we're also updating our transaction fee for subscribers who are retained for more than 12 months.

Announcing the Google Play Security Reward Program
At Google, we have long enjoyed a close relationship with the security research community. Today we're introducing the Google Play Security Reward Program to incentivize security research into popular Android apps, including Google's own apps. The program will help us find vulnerabilities and notify developers via security recommendations on how to fix them. We hope to bring the success we have with our other reward programs, and we invite developers and the research community to work together with us on proactively improving Google Play ecosystem's security.
Stay up to date with Google Play news and tips
★ ★ ★ ★ ★





 Jichao Li, Software Engineer; Shobana Ravi, Software Engineer
Jichao Li, Software Engineer; Shobana Ravi, Software Engineer