Hello All,
The Beta channel has been updated to ChromeOS version 15823.30.0 with Chrome Browser version 124.0.6367.66 for most ChromeOS devices.
If you find new issues, please let us know one of the following ways:
- File a bug
- Visit our Chrome OS communities
- General: Chromebook Help Community
- Beta Specific: ChromeOS Beta Help Community
- Report an issue or send feedback on Chrome
 Learn how to use Google’s AI tools to get organized.
Learn how to use Google’s AI tools to get organized.
 Rolling out this week, download Chrome on your Arm-compatible Windows PCs powered by Snapdragon for faster browsing on the web.
Rolling out this week, download Chrome on your Arm-compatible Windows PCs powered by Snapdragon for faster browsing on the web.
 We’re bringing real-time security capabilities to Safe Browsing’s Standard protection mode and sharing updates to Password Checkup on iOS.
We’re bringing real-time security capabilities to Safe Browsing’s Standard protection mode and sharing updates to Password Checkup on iOS.
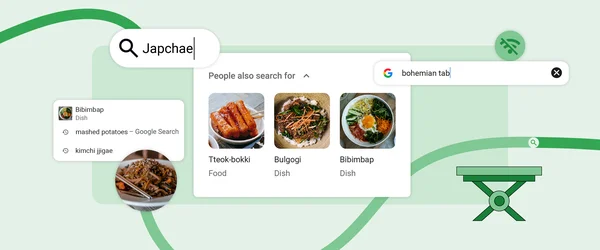 Chrome is improving search suggestions on desktop and mobile with images and popular topics based on what others are looking for.
Chrome is improving search suggestions on desktop and mobile with images and popular topics based on what others are looking for.
 We’re sharing six experiences to check out at MWC 2024, including our latest AI technologies and multi-device experiences.
We’re sharing six experiences to check out at MWC 2024, including our latest AI technologies and multi-device experiences.