While online accounts allow nonprofits to easily communicate with partners, volunteers and donors across the world, this shared network can also leave your account vulnerable to intruders. As your nonprofit continues to grow its online presence, it’s crucial to keep confidential information (e.g., finances or donor’s information) safe. While passwords have historically been the sole guardian for online account access, research from Google has shown that many passwords and security questions can easily be guessed. That's why we strongly recommend that all nonprofits using GSuite for Nonprofits, or Google products like Gmail, use 2-Step Verification (2SV) as an additional protection on their account(s).
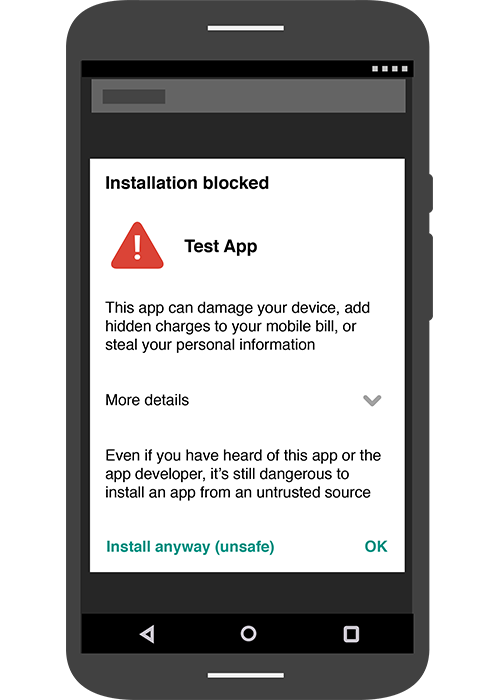
Account hijacking—a process through which an online account is stolen or hijacked by a hacker—constitutes a serious threat to your nonprofit’s operations. Typically, account hijackings are carried out by phishing attempts or hackers who guess weak passwords. Because of this, it’s especially important for your nonprofit to maintain strong and unique account passwords to keep sensitive data safe.
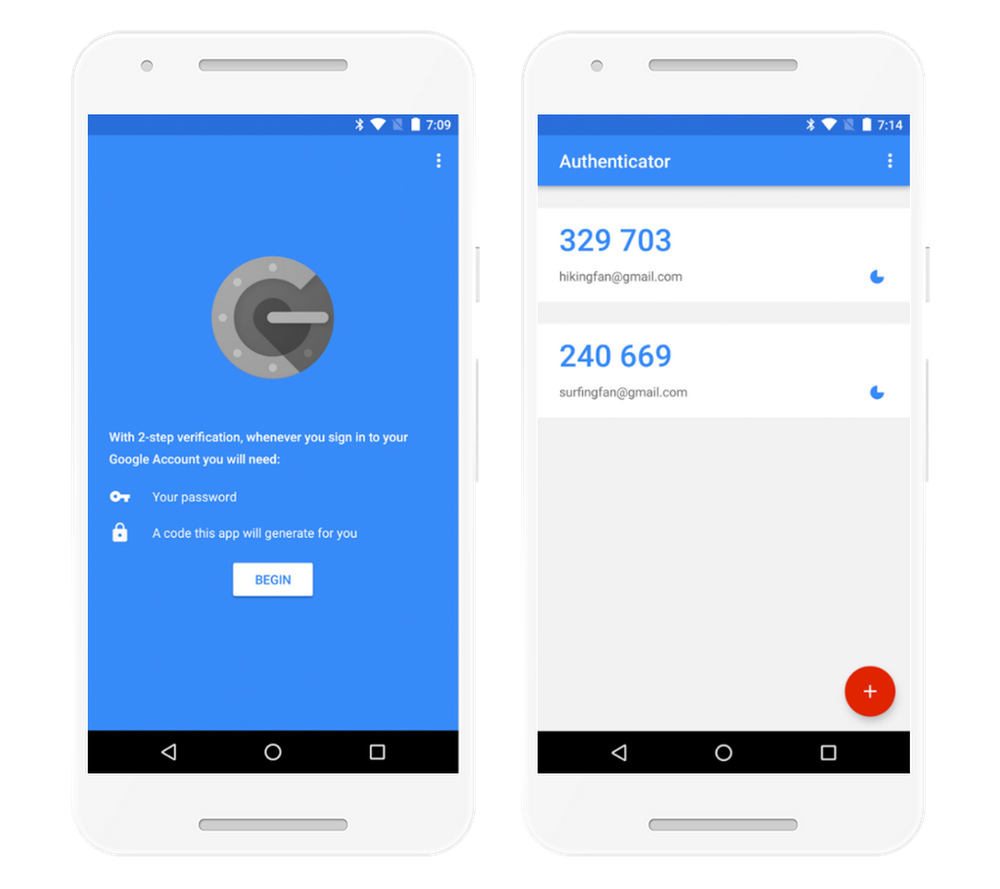
But 2SV goes beyond just a strong password. It's an effective security feature that combines "something you know" (e.g., a password) and "something you have" (e.g., a text, a prompt, or a Security Key) to protect your accounts. Think of this like withdrawing money from an ATM/cash machine: You need both your PIN and your debit card.
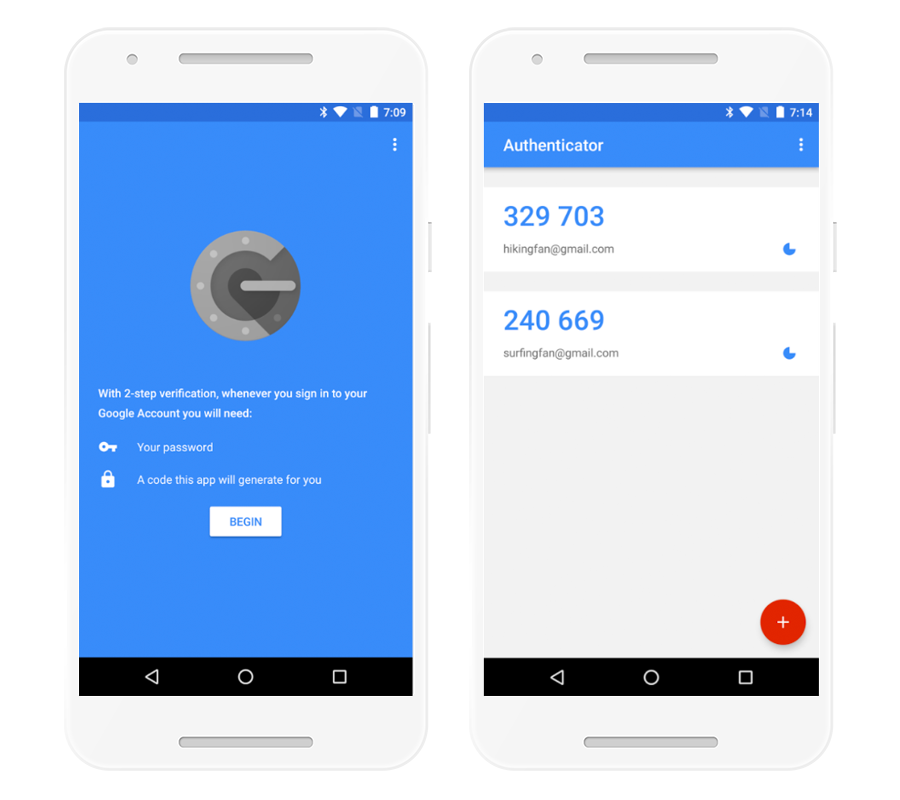
Now that you know what 2SV is, head over to our Help Page to start improving your nonprofit’s online security now. (Quick tip: Remember to keep your account settings up to date and configure backup options to use if your phone is ever lost or stolen). Stay safe, nonprofits!
To see if your nonprofit is eligible to participate, review the Google for Nonprofits eligibility guidelines. Google for Nonprofits offers organizations like yours access to Google tools like Gmail, Google Calendar, Google Drive, Google Ad Grants, YouTube for Nonprofits and more at no charge. These tools can help you reach new donors and volunteers, work more efficiently, and tell your nonprofit’s story. Learn more and enroll here.