This week, McKinsey released a report titled “Making a secure transition to the public cloud,” the result of interviews with IT security experts at nearly 100 enterprises around the world. Leveraging the expertise of Google Cloud and McKinsey security experts, the research presents a strategic framework for IT security in cloud and hybrid environments, and provides recommendations on how to migrate to the cloud while keeping security top of mind.
The research shows what many already know: that public cloud adoption is accelerating thanks to increased technical flexibility, simpler scaling, and lower operating costs. What’s exciting is that the research also reveals that many Chief Information Security Officers (CISOs) no longer view security as an inhibitor to adoption but instead an opportunity—“In many cases [CISOs] acknowledge that cloud service providers’ security resources dwarf their own,” the authors write—and now these companies are focused on how to best adopt and configure cloud services for increased security.
When implemented properly, public-cloud adoption can significantly reduce the total cost of ownership (TCO) for IT security.
This requires enterprises, cloud providers, and third-party service providers to work together collaboratively and transparently within a shared security model. Google Cloud has long believed in creating trust through transparency, previously releasing a detailed overview of our infrastructure security, explaining our shared responsibility model, and how we already protect our users and customers at the lower layers of the stack—and we’re thrilled to see McKinsey’s detailed endorsement of the same approach.
Common security approaches, and their tradeoffs.
Every company has different IT needs, but the report found two common security decisions companies take when adopting cloud services: (1) defining the perimeter, and (2) deciding whether to re-architect applications for greater manageability, performance, and security in the cloud (interestingly, only 27% of companies surveyed actually do this—change is hard).
The research identifies three common archetypes for perimeter security: backhauling, cleansheeting, and adopting cloud provider controls by default.
Backhauling allows companies to continue managing IT security on-prem, with an external gateway connecting the data center to the public cloud. Approximately half of the companies surveyed currently use this model, but only 11% plan to continue doing so, since it can keep companies from realizing certain cloud benefits, such as agility.
Cleansheeting requires greater investment and expertise, as it calls for redesigning IT security around a “virtual perimeter” and leveraging multiple cloud-native tools and services.
Using cloud provider controls is the most cost-effective solution, but—depending on the cloud provider—can limit autonomy and may offer limited capabilities.
McKinsey uses these three models, along with the decision to re-architect applications for the cloud, to identify six “archetypes” for cloud security. Each archetype has its own tradeoffs:
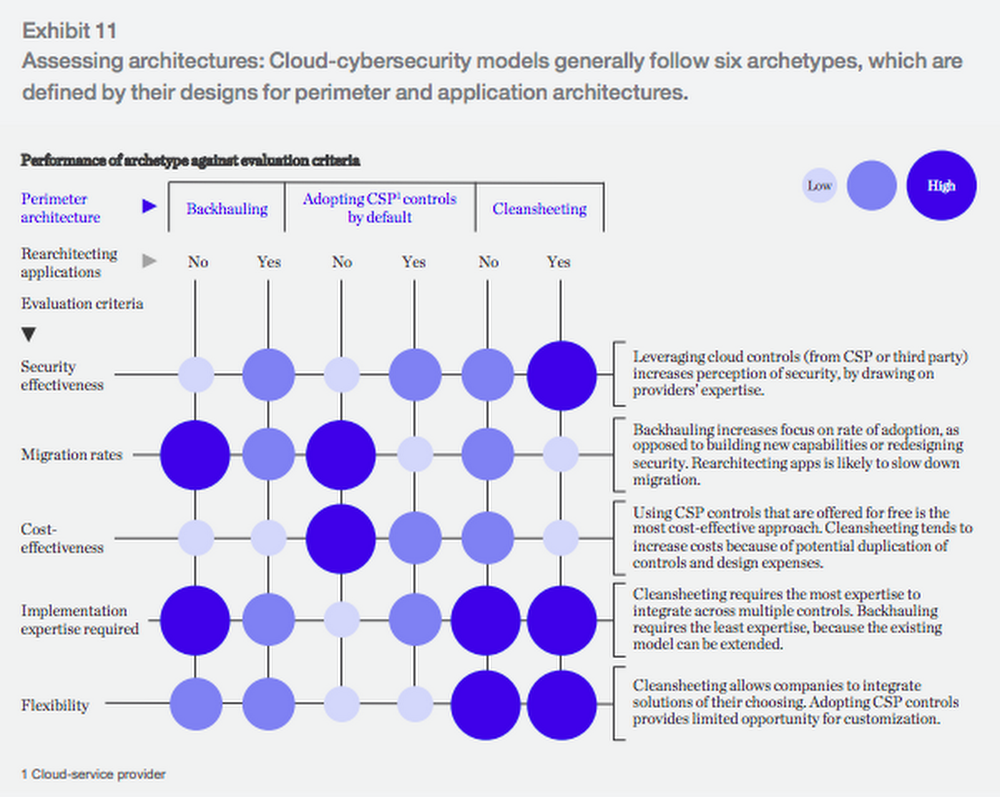
There isn’t a “right answer” for security when making a move to the cloud—it depends on your company’s expertise, flexibility, and cost decisions.
And, you don’t have to use only one archetype. For example, Evernote describes in their migration story to Google Cloud Platform:
“For most of our controls we found an equivalent, cloud platform version. For data encryption at rest, we gained a security control that we hadn’t engineered on our own. For some controls, like IP whitelisting, we had to adapt our security architecture to not rely on traditional network controls.”
— Rich Tener, Director of Security, Evernote
The economics of cloud security.
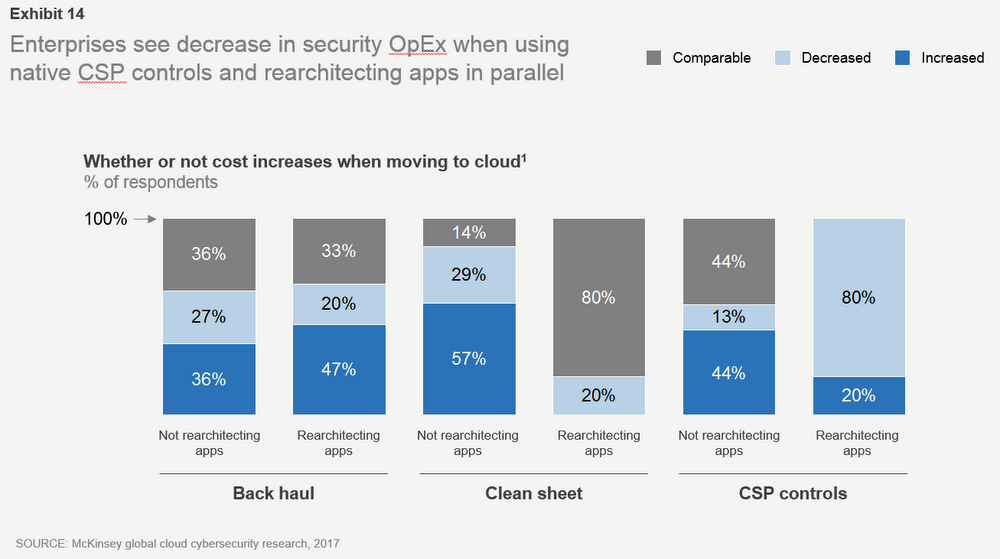
Relying on cloud service provider security controls is “the most cost-effective approach,” the authors write. “As organizations move more and more applications to the public cloud and lean towards using native CSP controls, a decrease in security operating and capex costs is likely.” Eighty percent of companies that choose to rely primarily on the cloud provider’s controls and re-architect their applications in parallel see cost savings.
So, if you’re planning a cloud migration, where should you focus your security efforts? McKinsey asked respondents about their approach to applying cloud security controls in several areas to find out what companies are doing:
Identity & access management (IAM): 60% of enterprises are using on-premises IAM solutions; in just three years respondents expect that number to be cut in half. At Google, we provide a tool called Google Cloud Directory Sync, which helps users bring existing identities to Google Cloud and manage cloud permissions natively with IAM.
Encryption: The majority of respondents encrypt data both at rest and in transit—and even more (upwards of 80% in both categories) will do so three years from now. Google Cloud already encrypts data at rest by default, and in transit when it crosses a physical boundary.
Perimeter security: Today, 40% of enterprises are backhauling data traffic and using existing on-premises network security controls—but that will decrease, with only 13% expecting to be using the same approach in 3 years. To help enterprises make the move to cloud-based perimeter control, Google Cloud lets users connect to their on-premises environment using Dedicated Interconnect, an IPsec VPN tunnel, direct peering or carrier peering. Google Cloud users can also control their perimeter with a Virtual Private Cloud (VPC).
Application security: 65% of respondents define security configuration standards for cloud-based applications, but less than 20% are using tools or template-based enforcement. To address this, Google Cloud offers Cloud Security Scanner, an automated way to scan apps for common vulnerabilities.
Operational monitoring: 64% of respondents use existing SIEM tools to monitor cloud applications rather than creating a new set for the cloud. Google Cloud users can export logs from Stackdriver to the SIEM of their choice.
Server-side endpoints: 51% of respondents have a high level of confidence in their cloud service provider’s approach to server-side endpoint security. Google Cloud customers can use a variety of partner tools for endpoint security.
User endpoints: 70% of respondents believe that public-cloud adoption will require changes to user endpoints. Google created the BeyondCorp enterprise security model to allow its employees to work from anywhere, and our customers can do the same with Identity Aware Proxy. In addition, Chromebooks provide automatic software updates, and run applications in a restricted sandbox.
Regulatory governance: When adopting public cloud, companies must navigate governance and compliance requirements, with data location and financial regulations topping respondents’ list of concerns. Google Cloud has a broad spectrum of compliance, including PCI, SOX, and HIPAA.
The report also includes a tactical 10-step plan for successful cloud migration. To learn more, download the full report.